Hi Folks, Welcome to another exciting Blog.
In the previous blog, we learned about "The Enarx Project" an open-source framework for running applications in TEEs (Trusted Execution Environments) using WebAssemby. It is the part of Confidential Computing Consortium from the Linux Foundation. But today we'll try hands on Enarx application using Cryptle.
Enarx in brief
Enarx aims to minimize the trust relationships required when executing applications, meaning that the only components which need to be trusted are: the CPU and associated firmware, the workload itself, and the Enarx middleware, which is fully open source and auditable. Applications run without any of the layers in the stack (e.g. hypervisor, kernel, user-space) being able to look into or alter the Keep or its contents.
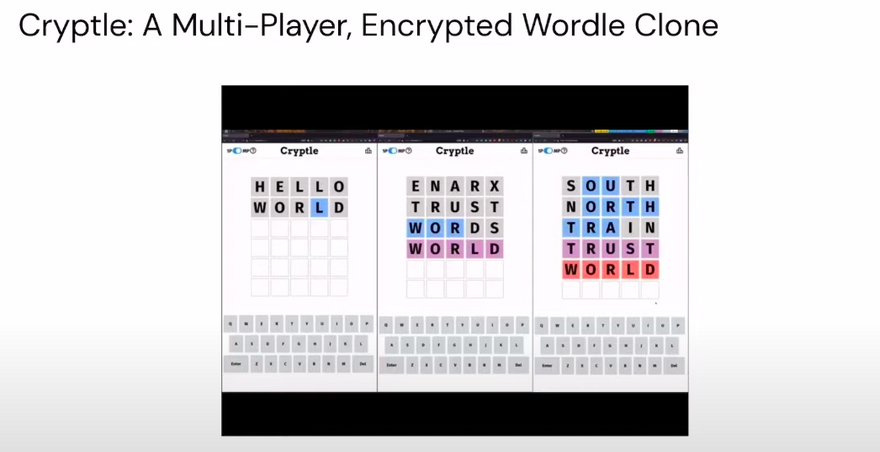
Today, we will deep dive into Cryptle - a Wordle clone for Enarx. The Cryptle game is developed using Rust on the server-side and JavaScript on the client-side. It can either be run on wasmtime which is not secure or on Enarx a trusted secure platform.
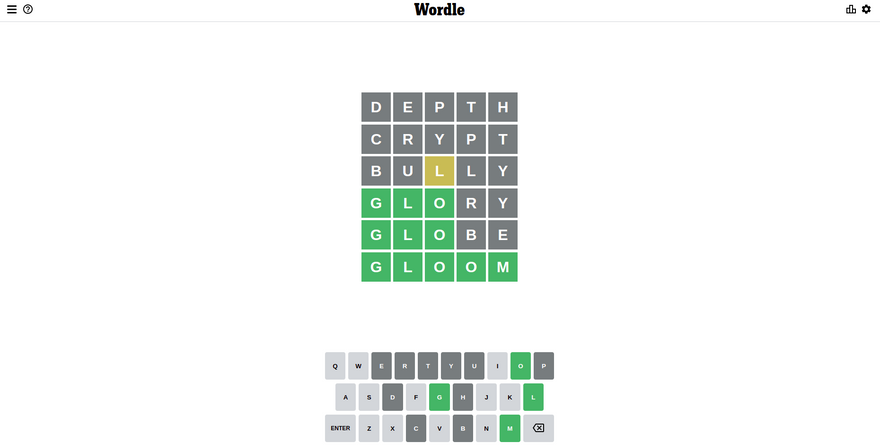
Wordle
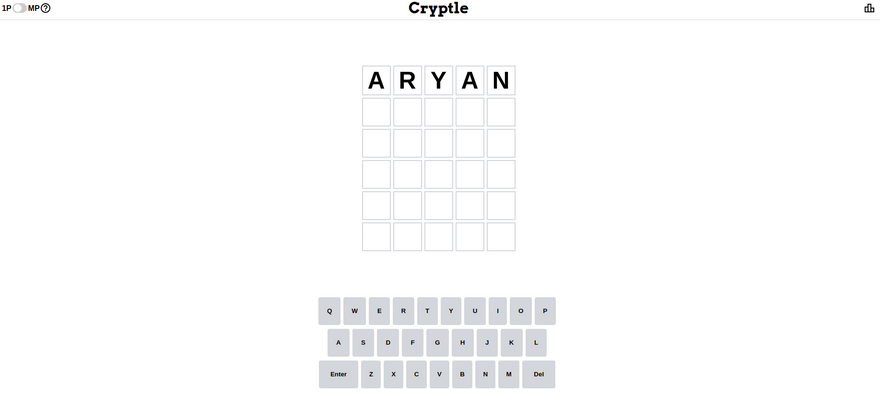
In Addition Cryptle has a multiplayer support
Steps to run Cryptle on your Machine
1) Install Rust
curl --proto '=https' --tlsv1.2 -sSf https://sh.rustup.rs | sh -s -- --default-toolchain nightly -y
source $HOME/.cargo/env
2) Install Enarx
git clone https://github.com/enarx/enarx
cd enarx/
cargo build
cargo install --bin enarx --path ./
3) Clone and Run Cryptle
git clone https://github.com/enarx/cryptle.git
cd cryptle/
cd Rust/
CARGO_TARGET_WASM32_WASI_RUNNER="wasmtime run --tcplisten 127.0.0.1:8443 --env FD_COUNT=1" cargo +nightly run --target wasm32-wasi
Server is running on http://127.0.0.1:8443.
Cryptle
The goal of Cryptle is to demonstrate data encryption in use, where the processing of the data is done in a Trusted Execution Environment (TEE), and only accessible to the Cryptle application.
The Single Player mode is similar to Wordle. A player has to guess a five-letter secret word (selected by the application), with yellow/green colored titles shown as hints in each round, indicating letters that match with the secret word.
In the Multi Player mode, the secret word is not selected by the application itself, but instead is (or rather are) suggested by the players themselves. Each player proposes words that are most likely to match those sent by others. The words are sent to the Cryptle application running in an Enarx Keep (a specific TEE instance) and are only revealed to the players when there’s a match between the secret words.
Standard engagement with the game involves playing Cryptle from the client-side and guessing the secret words.
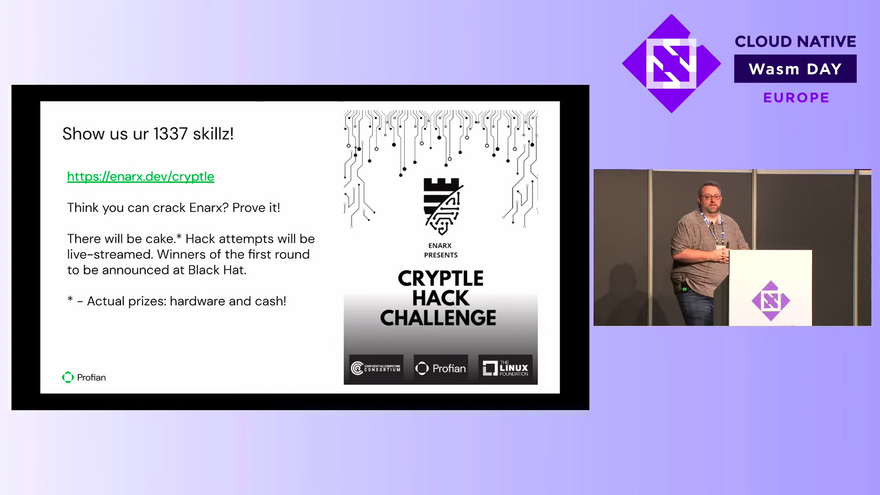
The Cryptle Hack Challenge
Alternatively, players may also write their own application that run on the host side and attempts to deduce or otherwise guess the secret words. Implementers have the option to choose a mechanism, but the application must be publicly available (under an OSI license) on GitHub or GitLab. Any programming language may be used, but it should not be intentionally obscured. All root privileges should be granted to the application. It should be documented how the application can derive the secret words or guess them. Applications will be executed as ELF binaries on a host running a modern Linux kernel. There will be no physical access allowed to the host.
Profian CTO- Mr. Nathaniel McCallum announcing The Cryptle Hack Challenge at CloudNativecon'22.
You can still win prizes if you can hack Cryptle and report it to the team. Reach us out via our Chat.
References:
- https://github.com/enarx/cryptle
- https://www.wasm.builders/nick/cryptle-a-secure-multi-party-wordle-clone-with-enarx-3cg9
- https://www.nytimes.com/games/wordle/index.html
- https://github.com/enarx/enarx
- https://enarx.dev/
- https://www.youtube.com/watch?v=353mpfL8r3s&list=PLj6h78yzYM2Ni0u-ONljTkv4uOutyjwq9&index=8&t=1023s
Do comment your ideas and suggestions related to the blog and please share if you found it useful.






Top comments (0)